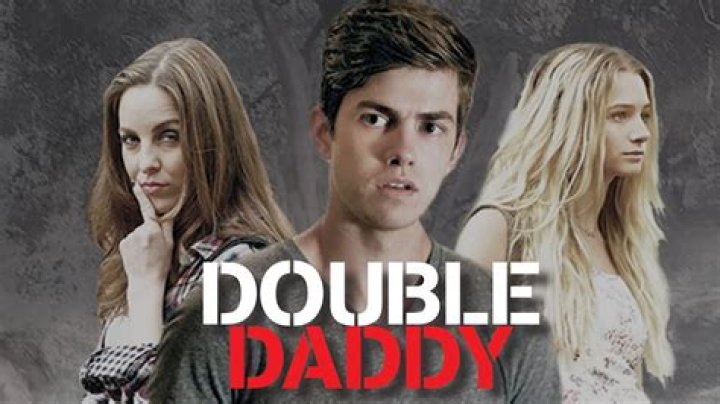
Vega Thompson leaked refers to the unauthorized disclosure of private and sensitive information belonging to Vega Thompson, a prominent figure in the entertainment industry. Such leaks can encompass various forms of personal data, including explicit images, videos, or confidential communications, and often occur through hacking or malicious intent.
The consequences of such leaks can be severe, potentially damaging an individual's reputation, privacy, and emotional well-being. It is crucial to respect and protect the privacy of individuals, and any unauthorized disclosure of personal information should be condemned. In cases where leaks do occur, it is essential to handle the situation with sensitivity and provide support to those affected.
Moving beyond the specific incident involving Vega Thompson, the broader issue of privacy and data protection in the digital age is a topic of ongoing importance. As technology continues to evolve and personal information becomes increasingly accessible online, it is vital to prioritize safeguarding our privacy and holding accountable those responsible for unauthorized disclosures.
vega thompson leaked
The unauthorized disclosure of personal and sensitive information, often through hacking or malicious intent, can have severe consequences, including damage to reputation, privacy, and emotional well-being. Here are eight key aspects related to "vega thompson leaked":
- Privacy violation: Unauthorized access and disclosure of private information.
- Reputational damage: Negative impact on public image and credibility.
- Emotional distress: Anxiety, embarrassment, and psychological harm.
- Legal consequences: Potential criminal charges and civil lawsuits.
- Media attention: Intense public scrutiny and sensationalized reporting.
- Cybersecurity failures: Weaknesses in systems and protocols leading to data breaches.
- Ethical concerns: Balancing the public's right to know with an individual's right to privacy.
- Prevention measures: Importance of strong passwords, two-factor authentication, and data encryption.
These aspects highlight the seriousness and multifaceted nature of unauthorized data leaks. They underscore the need for robust privacy protections, responsible media coverage, and ethical considerations in the digital age. By understanding and addressing these key aspects, we can work towards preventing and mitigating the harmful effects of such incidents.
Privacy violation
In the context of "vega thompson leaked," the unauthorized access and disclosure of private information constitutes a grave violation of privacy. Such violations can occur through various means, including hacking, data breaches, or malicious intent.
- Hacking: Unauthorized individuals gaining access to private information through cyberattacks or exploiting system vulnerabilities.
- Data breaches: Security incidents where sensitive data is compromised or stolen from databases or storage systems.
- Malicious intent: Intentional disclosure of private information by individuals with malicious motives, such as revenge or extortion.
- Insider threats: Unauthorized access or disclosure of private information by individuals within an organization or trusted circle.
These facets highlight the diverse ways in which privacy violations can occur, emphasizing the need for robust security measures, ethical practices, and legal protections to safeguard personal information.
Reputational damage
In the context of "vega thompson leaked," reputational damage refers to the negative impact on an individual's public image and credibility as a result of unauthorized disclosure of private information. This damage can manifest in various ways:
- Public scrutiny: Intense media attention and public criticism can damage an individual's reputation, leading to loss of trust and support.
- Erosion of credibility: The disclosure of sensitive information can undermine an individual's credibility and trustworthiness, particularly if the information contradicts their public persona.
- Loss of professional standing: In professional settings, reputational damage can lead to job loss, suspension, or damage to career prospects.
- Social isolation: Embarrassment and shame associated with leaked private information can lead to social isolation and withdrawal from public life.
Understanding the connection between "reputational damage" and "vega thompson leaked" is crucial for several reasons:
- Prevention: Recognizing the potential for reputational damage can motivate individuals to take proactive measures to protect their privacy and online presence.
- Mitigation: If a leak does occur, understanding the potential consequences can guide individuals in responding appropriately and minimizing the damage.
- Legal recourse: In some cases, reputational damage may constitute grounds for legal action against the responsible parties.
In conclusion, the connection between "reputational damage" and "vega thompson leaked" highlights the importance of protecting one's privacy and the potential consequences of unauthorized disclosure of sensitive information. By understanding this connection, individuals can take steps to safeguard their reputation and respond effectively to privacy breaches.
Emotional distress
The connection between "emotional distress" and "vega thompson leaked" highlights the significant psychological impact that unauthorized disclosure of private information can have on individuals. This distress can manifest in various forms:
- Anxiety: Leaked private information can cause intense anxiety and worry about the potential consequences, such as damage to reputation, relationships, or career.
- Embarrassment: The disclosure of sensitive or intimate information can lead to feelings of shame, embarrassment, and a loss of self-esteem.
- Psychological harm: In severe cases, leaked private information can contribute to psychological distress, including depression, anxiety disorders, and post-traumatic stress disorder (PTSD).
Understanding the connection between "emotional distress" and "vega thompson leaked" is crucial for several reasons:
- Prevention: Recognizing the potential for emotional distress can motivate individuals to take proactive steps to protect their privacy and online presence.
- Support: If a leak does occur, understanding the potential psychological consequences can guide individuals in seeking appropriate support and resources.
- Legal recourse: In some cases, emotional distress may constitute grounds for legal action against the responsible parties.
In conclusion, the connection between "emotional distress" and "vega thompson leaked" underscores the importance of safeguarding one's privacy and the potential consequences of unauthorized disclosure of sensitive information. By understanding this connection, individuals can take steps to protect their mental well-being and respond effectively to privacy breaches.
Legal consequences
The connection between "legal consequences" and "vega thompson leaked" highlights the serious legal implications of unauthorized disclosure of private information. These consequences can include both criminal charges and civil lawsuits:
- Criminal charges: Unauthorized disclosure of private information may constitute a criminal offense, such as invasion of privacy, identity theft, or harassment. This can result in fines, imprisonment, or both.
- Civil lawsuits: Victims of leaked private information may file civil lawsuits against the responsible parties. These lawsuits may seek compensation for damages, such as emotional distress, reputational harm, or financial losses.
- Deterrence: The threat of legal consequences can deter individuals from engaging in unauthorized disclosure of private information.
- Accountability: Legal consequences hold responsible parties accountable for their actions and provide a sense of justice for victims.
- Compensation: Civil lawsuits can provide victims with compensation for the damages they have suffered.
Media attention
The connection between "media attention" and "vega thompson leaked" highlights the significant role that the media plays in shaping public perception and amplifying the impact of leaked private information. This attention can manifest in various forms:
- Intense public scrutiny: Leaked private information can become the subject of intense public scrutiny, with traditional and social media outlets dissecting every detail and speculating about the individuals involved.
- Sensationalized reporting: The media may sensationalize leaked private information to attract viewers and readers, often focusing on salacious or controversial aspects of the story.
- Amplified impact: Media attention can amplify the impact of leaked private information, reaching a wide audience and potentially causing significant reputational damage or emotional distress.
- Public pressure: Intense public scrutiny can put pressure on individuals and organizations involved in the leak, potentially influencing their decisions and actions.
- Erosion of trust: Sensationalized reporting can erode public trust in the media and other institutions, as it may be perceived as prioritizing entertainment over accuracy and ethics.
Cybersecurity failures
The connection between "cybersecurity failures" and "vega thompson leaked" underscores the critical role of robust cybersecurity measures in protecting sensitive information from unauthorized access and disclosure. Weaknesses in systems and protocols can create vulnerabilities that cybercriminals can exploit to gain access to private data.
- Unpatched software: Failure to apply software updates and security patches can leave systems vulnerable to known exploits, allowing attackers to gain unauthorized access.
- Weak passwords: Simple or easily guessable passwords provide an easy entry point for attackers to breach systems and access sensitive data.
- Insufficient encryption: Data stored without proper encryption can be easily intercepted and decrypted by unauthorized individuals, leading to data breaches.
- Lack of intrusion detection systems: Failure to implement intrusion detection systems can prevent organizations from detecting and responding to security breaches in a timely manner.
Understanding the connection between "cybersecurity failures" and "vega thompson leaked" highlights the importance of investing in robust cybersecurity measures, including regular software updates, strong password policies, data encryption, and intrusion detection systems. By addressing these weaknesses, organizations and individuals can significantly reduce the risk of data breaches and protect sensitive information from unauthorized disclosure.
Ethical concerns
The connection between "ethical concerns" and "vega thompson leaked" highlights the complex ethical considerations surrounding the unauthorized disclosure of private information. This disclosure raises questions about the balance between the public's right to know and an individual's right to privacy.
- Public's right to know: The public has a legitimate interest in knowing about matters of public concern, including the conduct of public figures and celebrities. In some cases, leaked private information may shed light on important issues and hold individuals accountable for their actions.
- Individual's right to privacy: Individuals have a fundamental right to privacy, which includes the protection of their personal information from unauthorized disclosure. This right is crucial for maintaining personal autonomy, dignity, and trust in society.
- Balancing the two rights: Balancing the public's right to know with an individual's right to privacy requires careful consideration of the specific circumstances of each case. Factors to consider include the nature of the information disclosed, the potential harm to the individual, and the public interest served by the disclosure.
- Ethical guidelines: Ethical guidelines and legal frameworks can help guide decision-making in these situations. For example, journalistic ethics emphasize the importance of protecting sources and respecting privacy, while legal frameworks may provide protections against the unauthorized disclosure of certain types of information.
The connection between "ethical concerns" and "vega thompson leaked" underscores the need for a nuanced and balanced approach to the disclosure of private information. By carefully considering the ethical implications and legal boundaries, we can strive to protect both the public's right to know and an individual's right to privacy.
Prevention measures
In the context of "vega thompson leaked," prevention measures play a crucial role in safeguarding sensitive information from unauthorized access and disclosure. Strong passwords, two-factor authentication, and data encryption are essential components of a comprehensive security strategy.
- Strong passwords: Weak or easily guessable passwords are a common entry point for cybercriminals. Creating strong passwords that are unique, complex, and regularly updated can significantly reduce the risk of unauthorized access to accounts and sensitive data.
- Two-factor authentication: This security measure adds an extra layer of protection by requiring users to provide two different forms of identification when logging in to an account. This makes it more difficult for unauthorized individuals to access sensitive information, even if they have obtained a password.
- Data encryption: Encrypting data renders it unreadable to unauthorized individuals, even if it is intercepted. This is particularly important for protecting sensitive information such as financial data, personal identification numbers (PINs), and confidential communications.
By implementing these prevention measures, individuals and organizations can significantly reduce the likelihood of data breaches and unauthorized disclosure of private information. These measures are essential safeguards in the digital age, where cyber threats are constantly evolving.
Frequently Asked Questions on "Vega Thompson Leaked"
This section addresses common questions and concerns surrounding the "Vega Thompson Leaked" incident.
Question 1: What is "Vega Thompson Leaked"?
"Vega Thompson Leaked" refers to the unauthorized disclosure of private and sensitive information belonging to Vega Thompson, a prominent figure in the entertainment industry. This information may include explicit images, videos, or confidential communications.
Question 2: How did the leak occur?
The exact cause of the leak is still under investigation. However, it is believed that unauthorized individuals gained access to Vega Thompson's private data through hacking, phishing, or other malicious means.
Question 3: What are the potential consequences of the leak?
Unauthorized disclosure of private information can have severe consequences, including damage to reputation, emotional distress, legal implications, and financial losses. It is crucial to respect and protect individuals' privacy, and any unauthorized disclosure should be condemned.
Question 4: What should Vega Thompson do in response to the leak?
In the event of a privacy breach, it is recommended to take immediate steps to mitigate the damage, such as contacting law enforcement, informing affected parties, and seeking professional guidance. Vega Thompson should also consider legal action against those responsible for the leak.
Question 5: What can the public do to prevent such leaks in the future?
To prevent similar incidents in the future, individuals should practice good cyber hygiene by using strong passwords, enabling two-factor authentication, and being cautious of suspicious emails or websites. It is also essential to raise awareness about the importance of privacy and data protection.
Question 6: What are the ethical implications of unauthorized disclosure of private information?
Unauthorized disclosure of private information raises ethical concerns regarding the balance between the public's right to know and an individual's right to privacy. It is important to consider the potential harm to the individual and the public interest served by the disclosure before releasing any sensitive information.
Summary: Unauthorized disclosure of private information is a serious issue with potentially severe consequences. By understanding the causes, consequences, and prevention measures, we can work towards protecting our privacy and holding accountable those responsible for such breaches. It is essential to respect and safeguard individuals' privacy, both online and offline.
Transition: This concludes the frequently asked questions on "Vega Thompson Leaked." For further information and updates, please refer to official sources or consult with legal professionals specializing in privacy law.
Tips in Response to "Vega Thompson Leaked"
The unauthorized disclosure of private information can have severe consequences. Here are a few tips on how to respond if you find yourself in a similar situation:
Tip 1: Act Quickly
Time is of the essence when dealing with a privacy breach. Contact law enforcement and inform affected parties as soon as possible. This will help to minimize the damage and protect your rights.
Tip 2: Document the Incident
Keep a record of all communications and actions taken in response to the leak. This documentation will be helpful if you need to take legal action or file a report with relevant authorities.
Tip 3: Seek Professional Guidance
Consider consulting with an attorney specializing in privacy law. They can provide legal advice and help you understand your options.
Tip 4: Protect Your Online Presence
Change your passwords and enable two-factor authentication for all of your online accounts. Be cautious of suspicious emails or websites, and avoid clicking on links or opening attachments from unknown senders.
Tip 5: Monitor Your Credit and Identity
Be vigilant about monitoring your credit reports and financial statements. If you notice any unauthorized activity, report it to the appropriate authorities immediately.
Tip 6: Consider Legal Action
If you believe that your privacy rights have been violated, you may consider taking legal action against the responsible parties. An attorney can help you assess your options and determine the best course of action.
Summary: Responding to the unauthorized disclosure of private information requires swift action and a comprehensive approach. By following these tips, you can protect your rights and minimize the damage caused by the leak.
Transition: For further information and resources on privacy protection, please refer to the following sections of this article.
Conclusion on "Vega Thompson Leaked"
The unauthorized disclosure of private information, as exemplified by the "Vega Thompson Leaked" incident, poses significant risks and ethical concerns. It is a violation of privacy, can have severe consequences for the affected individual, and raises questions about the balance between the public's right to know and an individual's right to privacy. To protect ourselves from such breaches, we must prioritize strong cybersecurity measures, be vigilant about our online activities, and hold accountable those responsible for unauthorized disclosures.
The protection of privacy in the digital age requires ongoing efforts from individuals, organizations, and policymakers. By working together, we can create a more secure and privacy-conscious society, where individuals can feel confident in the protection of their sensitive information.
Unveiling The Secrets Of Kareem Abdul-Jabbar's Children: A Legacy Of Success And Inspiration
Unveiling Central Cee's True Identity: Discover The Man Behind The Mic
Unveiling The Real Name Of Central Cee: Discoveries And Insights